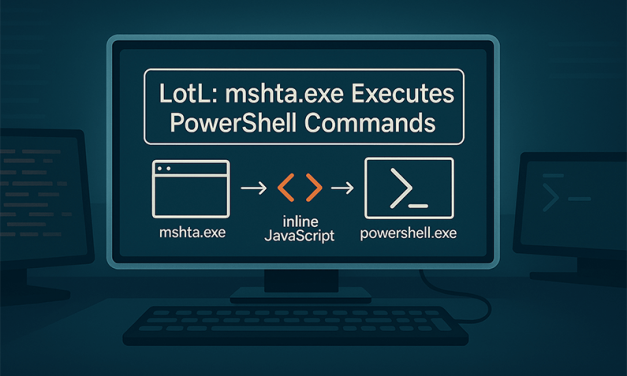
Fileless LotL Attacks: How mshta.exe Executes PowerShell Commands via Inline JavaScript
Oct 6, 2025 | Ethical Hacking | 0 |
Fileless attacks exploit trusted system binaries and execute payloads entirely in memory. One...
Read MoreLiving off the Land (LotL): Fileless PowerShell Attack Techniques
Oct 4, 2025 | Ethical Hacking | 0 |
In today’s cybersecurity landscape, attackers are getting smarter and stealthier....
Read MoreSysmon Explained: Setup, Configuration, and Log Forwarding to SIEM
Sep 10, 2025 | Ethical Hacking | 0 |
Learn what Sysmon is, how to install and configure it, and how to forward logs to SIEM tools like...
Read MoreHow to Enable Wazuh Archives and Configure Index Patterns
Sep 8, 2025 | Ethical Hacking | 0 |
When working with security operations center (SOC), Wazuh gives you powerful alerting and...
Read MoreFollow Us
Recent Posts
Recent Reviews
-
How to Install Kali Linux on a USB Flash Drive – Creating A Portable and Standalone Kali Bootable USB
Score: 90%
-
DOMAIN GENERATION ALGORITHM – DGA IN MALWARE
Score: 99%
-
Fast-Flux Networks in Cybersecurity: A Technique Used to Hide C2 Server IP Addresses
Score: 90%
-
Cyber Threat Intelligence (CTI): Definitive Guide for Beginners
Score: 85%
Subscribe
Subscribe To Our Newsletter
Join our mailing list to receive the latest news and updates from our team.













Subscribe To Our Newsletter
Join our mailing list to receive the latest news and updates from our team.
You have Successfully Subscribed!